For working professionals
For fresh graduates
- Study abroad
More
- Executive Doctor of Business Administration from SSBM
- Doctorate in Business Administration by Edgewood College
- Doctorate of Business Administration (DBA) from ESGCI, Paris
- Doctor of Business Administration From Golden Gate University
- Doctor of Business Administration from Rushford Business School, Switzerland
- Post Graduate Certificate in Data Science & AI (Executive)
- Gen AI Foundations Certificate Program from Microsoft
- Gen AI Mastery Certificate for Data Analysis
- Gen AI Mastery Certificate for Software Development
- Gen AI Mastery Certificate for Managerial Excellence
- Gen AI Mastery Certificate for Content Creation
- Post Graduate Certificate in Product Management from Duke CE
- Human Resource Analytics Course from IIM-K
- Directorship & Board Advisory Certification
- Gen AI Foundations Certificate Program from Microsoft
- CSM® Certification Training
- CSPO® Certification Training
- PMP® Certification Training
- SAFe® 6.0 Product Owner Product Manager (POPM) Certification
- Post Graduate Certificate in Product Management from Duke CE
- Professional Certificate Program in Cloud Computing and DevOps
- Python Programming Course
- Executive Post Graduate Programme in Software Dev. - Full Stack
- AWS Solutions Architect Training
- AWS Cloud Practitioner Essentials
- AWS Technical Essentials
- The U & AI GenAI Certificate Program from Microsoft
6. JDK in Java
7. C++ Vs Java
16. Java If-else
18. Loops in Java
20. For Loop in Java
46. Packages in Java
53. Java Collection
56. Generics In Java
57. Java Interfaces
60. Streams in Java
63. Thread in Java
67. Deadlock in Java
74. Applet in Java
75. Java Swing
76. Java Frameworks
78. JUnit Testing
81. Jar file in Java
82. Java Clean Code
86. Java 8 features
87. String in Java
93. HashMap in Java
98. Enum in Java
101. Hashcode in Java
105. Linked List in Java
109. Array Length in Java
111. Split in java
112. Map In Java
115. HashSet in Java
118. DateFormat in Java
121. Java List Size
122. Java APIs
128. Identifiers in Java
130. Set in Java
132. Try Catch in Java
133. Bubble Sort in Java
135. Queue in Java
142. Jagged Array in Java
144. Java String Format
145. Replace in Java
146. charAt() in Java
147. CompareTo in Java
151. parseInt in Java
153. Abstraction in Java
154. String Input in Java
156. instanceof in Java
157. Math Floor in Java
158. Selection Sort Java
159. int to char in Java
164. Deque in Java
172. Trim in Java
173. RxJava
174. Recursion in Java
175. HashSet Java
177. Square Root in Java
190. Javafx
Caesar Cipher Program in Java: A Complete Guide to Implementing Simple Encryption and Decryption
The Caesar cipher is one of the oldest encryption techniques, dating back to Julius Caesar who used it to protect military communications. This simple encryption method has become a fundamental concept in modern cryptography. In this guide, we'll explore how to create a caesar cipher program in java, understand its mechanics, and see practical applications.
A Caesar cipher works by shifting each letter in a message by a fixed number of positions in the alphabet. For example, with a shift of 3, 'A' becomes 'D', 'B' becomes 'E', and so on. Though simple, this encryption technique introduces key cryptographic concepts that form the foundation for more sophisticated encryption algorithms.
Enhance your Java skills with expert-led training. Check out upGrad’s Software Engineering course and learn how to apply Java in real-world projects.
How Caesar Cipher Works
The Caesar cipher uses a substitution method where each letter in the plaintext is replaced by a letter at a fixed position further down the alphabet. Here's the basic algorithm:
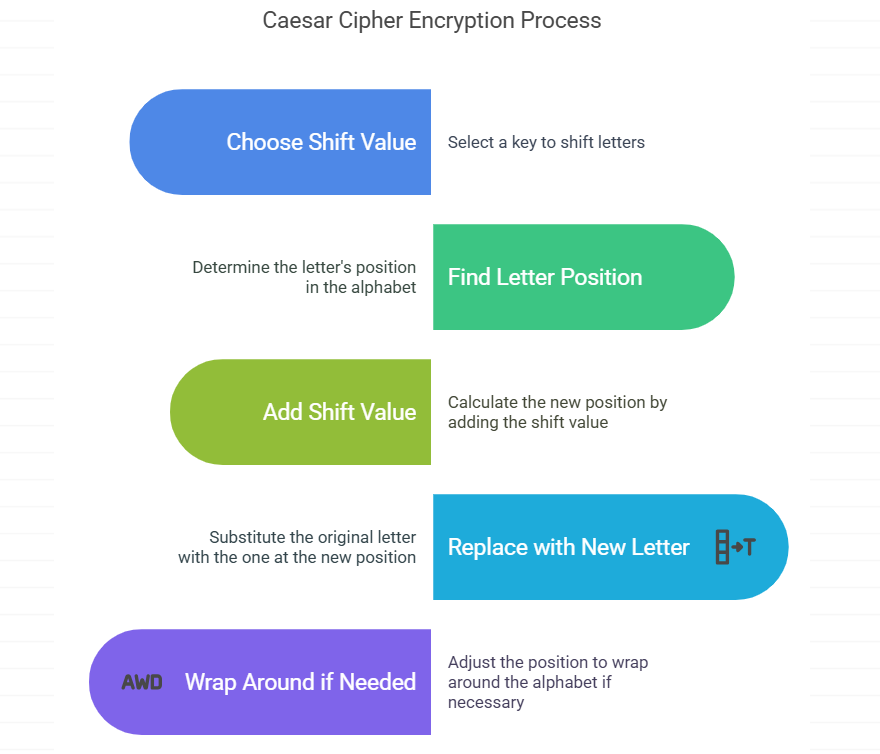
- Choose a shift value (the key).
- For each letter in the message:
- Find its position in the alphabet
- Add the shift value to get the new position
- Replace with the letter at the new position
- Wrap around to the beginning if needed (e.g. Z with shift 1 becomes A)
Java developers are in high demand—especially with cloud and DevOps skills. Gain both with this Professional Certificate Program by upGrad.
Simple Caesar Cipher Program in Java
Let's implement a basic caesar cipher program in java programming that can encrypt and decrypt messages.
public class SimpleCaesarCipher {
// Method to encrypt plaintext using Caesar Cipher
public static String encrypt(String plainText, int shift) {
StringBuilder result = new StringBuilder();
// For each character in the plainText
for (int i = 0; i < plainText.length(); i++) {
char ch = plainText.charAt(i);
// Apply encryption only to alphabetic characters
if (Character.isLetter(ch)) {
// Determine if character is uppercase
boolean isUpperCase = Character.isUpperCase(ch);
// Shift the character and wrap around if needed
ch = (char) (((int) ch + shift - (isUpperCase ? 65 : 97)) % 26 + (isUpperCase ? 65 : 97));
}
result.append(ch);
}
return result.toString();
}
// Method to decrypt ciphertext using Caesar Cipher
public static String decrypt(String cipherText, int shift) {
// Decryption is just encryption with negative shift
return encrypt(cipherText, 26 - (shift % 26));
}
public static void main(String[] args) {
String message = "HELLO WORLD";
int shift = 3;
// Encrypt the message
String encrypted = encrypt(message, shift);
System.out.println("Original message: " + message);
System.out.println("Encrypted message: " + encrypted);
// Decrypt the message
String decrypted = decrypt(encrypted, shift);
System.out.println("Decrypted message: " + decrypted);
}
}
Output:
Original message: HELLO WORLD
Encrypted message: KHOOR ZRUOG
Decrypted message: HELLO WORLD
This simple caesar cipher program in java successfully encrypts and decrypts messages using a specified shift value. The program handles both uppercase and lowercase letters while preserving non-alphabetic characters.
Advanced Caesar Cipher Implementation
For more practical applications, we need a better caesar cipher program in java. The following example includes handling for different character types and a more user-friendly interface.
import java.util.Scanner;
public class CaesarCipherProgram {
// Method to encrypt text using Caesar Cipher
public static String encrypt(String plaintext, int shift) {
StringBuilder result = new StringBuilder();
for (char character : plaintext.toCharArray()) {
// Process only alphabetic characters
if (Character.isLetter(character)) {
char base = Character.isUpperCase(character) ? 'A' : 'a';
// Apply shift and wrap around if needed
result.append((char) ((character - base + shift) % 26 + base));
} else {
// Keep non-alphabetic characters unchanged
result.append(character);
}
}
return result.toString();
}
// Method to decrypt text using Caesar Cipher
public static String decrypt(String ciphertext, int shift) {
// Decrypt by using the encryption method with a negative shift
return encrypt(ciphertext, 26 - (shift % 26));
}
public static void main(String[] args) {
Scanner scanner = new Scanner(System.in);
// Get user input
System.out.print("Enter a message to encrypt: ");
String message = scanner.nextLine();
System.out.print("Enter the shift value (1-25): ");
int shift = scanner.nextInt() % 26;
// Perform encryption
String encrypted = encrypt(message, shift);
System.out.println("\nEncrypted message: " + encrypted);
// Perform decryption
String decrypted = decrypt(encrypted, shift);
System.out.println("Decrypted message: " + decrypted);
scanner.close();
}
}
Output (Example):
Enter a message to encrypt: Meet me at the park
Enter the shift value (1-25): 7
Encrypted message: Tlla tl ha aol whyr
Decrypted message: Meet me at the park
This advanced caesar cipher program in java allows users to input their own messages and shift values, making it more interactive and practical for actual use.
Real-World Application of Caesar Cipher
Educational Tool for Cryptography Basics
Problem Statement: A computer science teacher needs to demonstrate basic encryption concepts to students in an interactive way. The teacher wants a simple program that can show the step-by-step encryption process.
import java.util.Scanner;
public class CaesarCipherEducational {
public static void main(String[] args) {
// Create scanner for user input
Scanner scanner = new Scanner(System.in);
// Get the message to encrypt from user
System.out.print("Enter a short message: ");
String message = scanner.nextLine();
// Get the shift value, ensuring it's within 0-25 range
System.out.print("Enter shift value: ");
int shift = scanner.nextInt() % 26;
// Visual separator for display clarity
System.out.println("\nEncryption Process:");
System.out.println("-------------------");
// Process each character in the message
for (char c : message.toCharArray()) {
if (Character.isLetter(c)) {
// Determine whether to use uppercase or lowercase ASCII offset
char base = Character.isUpperCase(c) ? 'A' : 'a';
// Apply the Caesar cipher formula: (letter position + shift) % 26
char encrypted = (char) ((c - base + shift) % 26 + base);
// Display the transformation of each letter
System.out.println(c + " → " + encrypted + " (Shift " + shift + " positions)");
} else {
// Non-alphabetic characters remain unchanged
System.out.println(c + " → " + c + " (Non-alphabetic character, no change)");
}
}
// Close scanner to prevent resource leak
scanner.close();
}
}
Output:
Enter a short message: Hello
Enter shift value: 3
Encryption Process:
-------------------
H → K (Shift 3 positions)
e → h (Shift 3 positions)
l → o (Shift 3 positions)
l → o (Shift 3 positions)
o → r (Shift 3 positions)
This educational tool helps students visualize how each character in a message is transformed during the encryption process, making the Caesar cipher concept easier to understand.
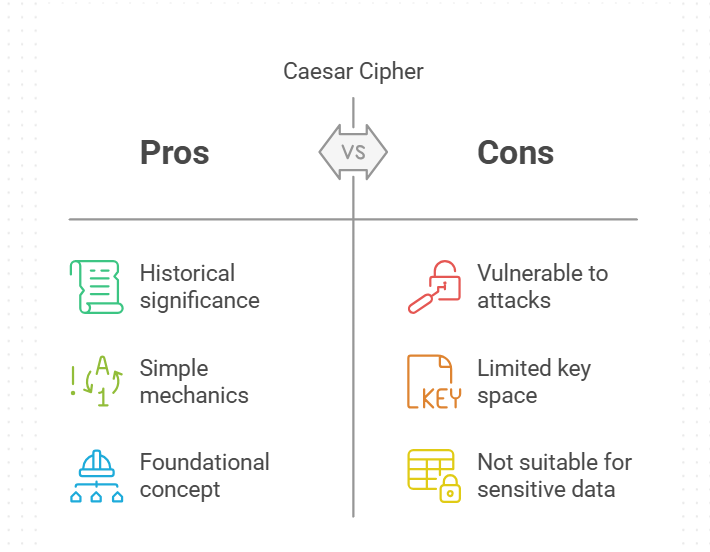
Where Caesar Cipher Is Used Today
Despite its simplicity and vulnerability to attacks, the Caesar cipher program in Java can be used in several scenarios:
- Teaching the fundamentals of cryptography
- Creating simple encoding challenges
- Hiding information from casual observers
- As a stepping stone to understanding advanced encryption
Conclusion
The Caesar cipher program in Java represents an excellent starting point for anyone interested in cryptography and encryption techniques. While it's not secure enough for modern applications, implementing this algorithm helps build a fundamental understanding of how encryption works. By exploring more advanced encryption methods, you can build upon the concepts learned from this simple yet historic cipher.
Whether you're a student learning about cryptography or a developer practicing Java programming, the Caesar cipher offers valuable insights into the world of secure communications. The simplicity of the caesar cipher program in java makes it an ideal introductory project for beginners while still illustrating core encryption principles.
Frequently Asked Questions
1. What is a Caesar cipher program in Java?
A Caesar cipher program in Java is a simple encryption tool that shifts each letter in a message by a fixed number of positions in the alphabet, creating a coded message that can be deciphered only if you know the shift value. This historical cipher was used by Julius Caesar to communicate with his generals on the battlefield.
2. How do I implement a simple Caesar cipher program in Java?
To implement a simple Caesar cipher in Java, create methods for encryption and decryption that iterate through each character, apply the appropriate shift, and handle wrapping around the alphabet when needed. Understanding modular arithmetic is crucial since it allows the program to cycle back to 'A' after reaching 'Z'.
3. Can Caesar cipher handle numbers and special characters?
Most basic Caesar cipher implementations leave numbers and special characters unchanged, though you can extend your program to handle these characters with custom rules. You might consider using ASCII values or creating separate lookup tables for different character sets to enhance the encryption.
4. What shift value provides the strongest encryption in Caesar cipher?
All shift values in a Caesar cipher offer equal (and minimal) security since there are only 25 possible keys to try. The strength lies not in the shift value but in keeping the shift secret. Historically, Caesar himself preferred a shift of 3, but this offers no cryptographic advantage over other values.
5. How can I break a Caesar cipher without knowing the shift?
Caesar ciphers can be broken using frequency analysis (analyzing which letters appear most often) or by simply trying all 25 possible shift values (brute force attack). In English, the letter 'E' occurs most frequently, which provides a starting point for frequency-based decryption attempts.
6. Is Caesar cipher suitable for modern security applications?
No, Caesar cipher is not suitable for modern security as it can be easily broken. It's primarily used for educational purposes to introduce encryption concepts. Modern systems use advanced algorithms like AES and RSA that employ mathematical principles far beyond simple character shifting.
7. Can I use Caesar cipher for file encryption in Java?
While technically possible, it's not recommended to use Caesar cipher for file encryption as it provides minimal security. Modern encryption algorithms are much more secure. If implementing it for learning purposes, remember to use FileInputStream and FileOutputStream classes to process file data byte by byte.
8. How does Caesar cipher relate to ROT13?
ROT13 is a specific type of Caesar cipher with a fixed shift of 13 positions. It's popular because applying it twice returns the original text (13+13=26, a full rotation). This property makes ROT13 particularly useful for hiding spoilers or solutions online that can be quickly decoded when needed.
9. What's the time complexity of a Caesar cipher algorithm?
The time complexity is O(n), where n is the length of the input text, as we process each character exactly once during encryption or decryption. This linear time complexity makes Caesar cipher very efficient computationally, even for large texts.
10. Can I use Unicode characters with Caesar cipher in Java?
Yes, you can adapt a Caesar cipher program in Java to work with Unicode characters by applying the shift to the character's Unicode value, though handling the much larger character set introduces additional complexity. Remember that Java's char type supports the full Unicode range, making implementation straightforward.
11. How do I handle uppercase and lowercase letters in Caesar cipher?
The best approach is to determine the base value ('A' or 'a') based on the case of each letter, then apply the shift while preserving the original case. Using the Character class methods like isUpperCase() and isLowerCase() makes this process clean and readable in your caesar cipher program in java.
-9cd0a42cab014b9e8d6d4c4ba3f27ab1.webp&w=3840&q=75)
Take the Free Quiz on Java
Answer quick questions and assess your Java knowledge


Author|900 articles published


upGrad Learner Support
Talk to our experts. We are available 7 days a week, 9 AM to 12 AM (midnight)
Indian Nationals
1800 210 2020
Foreign Nationals
+918068792934
Disclaimer
1.The above statistics depend on various factors and individual results may vary. Past performance is no guarantee of future results.
2.The student assumes full responsibility for all expenses associated with visas, travel, & related costs. upGrad does not provide any a.



