For working professionals
For fresh graduates
- Study abroad
More
- Executive Doctor of Business Administration from SSBM
- Doctorate in Business Administration by Edgewood College
- Doctorate of Business Administration (DBA) from ESGCI, Paris
- Doctor of Business Administration From Golden Gate University
- Doctor of Business Administration from Rushford Business School, Switzerland
- Post Graduate Certificate in Data Science & AI (Executive)
- Gen AI Foundations Certificate Program from Microsoft
- Gen AI Mastery Certificate for Data Analysis
- Gen AI Mastery Certificate for Software Development
- Gen AI Mastery Certificate for Managerial Excellence
- Gen AI Mastery Certificate for Content Creation
- Post Graduate Certificate in Product Management from Duke CE
- Human Resource Analytics Course from IIM-K
- Directorship & Board Advisory Certification
- Gen AI Foundations Certificate Program from Microsoft
- CSM® Certification Training
- CSPO® Certification Training
- PMP® Certification Training
- SAFe® 6.0 Product Owner Product Manager (POPM) Certification
- Post Graduate Certificate in Product Management from Duke CE
- Professional Certificate Program in Cloud Computing and DevOps
- Python Programming Course
- Executive Post Graduate Programme in Software Dev. - Full Stack
- AWS Solutions Architect Training
- AWS Cloud Practitioner Essentials
- AWS Technical Essentials
- The U & AI GenAI Certificate Program from Microsoft
5. Array in C
13. Boolean in C
18. Operators in C
33. Comments in C
38. Constants in C
41. Data Types in C
49. Double In C
58. For Loop in C
60. Functions in C
70. Identifiers in C
81. Linked list in C
83. Macros in C
86. Nested Loop in C
97. Pseudo-Code In C
100. Recursion in C
103. Square Root in C
104. Stack in C
106. Static function in C
107. Stdio.h in C
108. Storage Classes in C
109. strcat() in C
110. Strcmp in C
111. Strcpy in C
114. String Length in C
115. String Pointer in C
116. strlen() in C
117. Structures in C
119. Switch Case in C
120. C Ternary Operator
121. Tokens in C
125. Type Casting in C
126. Types of Error in C
127. Unary Operator in C
128. Use of C Language
Overflow And Underflow in C
In machine learning, computers do a lot of math to solve problems. Sometimes, they try different answers until they find the best one.
However, computers can't store every number exactly. They have to round numbers to fit them into memory. This rounding causes small mistakes called rounding errors.
Sometimes, a number can be too big for the computer to store, and that’s called overflow. Other times, a number can be too small to be stored, and that's called underflow.
Normally, these mistakes are small and don’t cause problems, but if there are too many calculations, the errors can add up and make the results wrong.
In this tutorial, you'll learn about overflow and underflow in computers, how they occur during calculations, and their impact on machine learning algorithms.
Improve your C programming skills with our Software Development courses — take the next step in your learning journey!
Overflow in C
Overflow in C happens when the result of a calculation exceeds the largest value that can be represented by the data type, causing it to be assigned an infinite value.
Example of Overflow:
#include <stdio.h>
int main() {
double a = 1e308; // A large number
double result = a * 10; // Overflow occurs here
printf("Result: %e\n", result); // Might print: Result: inf
return 0;
}
Output:
Result: inf
Explanation: Here, multiplying a very large number (1e308) by 10 exceeds the maximum value for a double. The result is inf, indicating overflow.
Also Read: What Are Storage Classes in C?
Now that you've learned about overflow in C, let’s dive into its opposite, Underflow in C, to understand how it can also cause problems in your program.
Underflow in C
When very small numbers (close to zero) are represented in a computer, they may be rounded to zero if they are smaller than the smallest value that can be represented with the given precision.
Example of Underflow:
#include <stdio.h>
int main() {
double a = 1e-300; // A very small number
double b = 1e-300;
double result = a * b; // Underflow occurs here
printf("Result: %e\n", result); // Might print: Result: 0.000000e+00
return 0;
}
Output:
Result: 0.000000e+00
Explanation: Here, multiplying two very small numbers results in an underflow. The output shows that the result is treated as 0.000000e+00, indicating that the value is too small to be represented.
Also Read: Python Vs C: Complete Side-by-Side Comparison
After grasping underflow, it's important to explore how both overflow and underflow affect specific functions, like the overflow and underflow in Softmax Function, which plays a key role in machine learning.
Overflow and Underflow in Softmax Function
Overflow and underflow can be problematic in machine learning algorithms like the softmax function. The softmax function is used to calculate probabilities for a classification problem, and large or small values in the input can lead to instability.
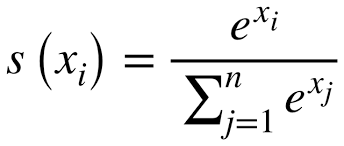
The softmax function is defined as:
Example of Numerical Instability: If all x_i values are very large or very small, exp(x_i) can either overflow or underflow, causing instability.
Here is the code to fix the softmax overflow and underflow issues:
#include <stdio.h>
#include <math.h>
void stable_softmax(double *x, int n, double *result) {
double max_val = x[0];
for (int i = 1; i < n; i++) {
if (x[i] > max_val) {
max_val = x[i];
}
}
double sum = 0;
for (int i = 0; i < n; i++) {
result[i] = exp(x[i] - max_val); // Subtract max to avoid overflow
sum += result[i];
}
for (int i = 0; i < n; i++) {
result[i] /= sum; // Normalize the result
}
}
int main() {
double x[] = {1000, 1000, 1000}; // Large values
int n = 3;
double result[n];
stable_softmax(x, n, result);
for (int i = 0; i < n; i++) {
printf("Softmax result[%d]: %.10f\n", i, result[i]);
}
return 0;
}
Output:
Softmax result[0]: 0.3333333333
Softmax result[1]: 0.3333333333
Softmax result[2]: 0.3333333333
Explanation: By subtracting the maximum value (max_val) from the input values, we prevent overflow or underflow when calculating exp(x_i). This ensures that the softmax function remains numerically stable and returns the correct probabilities.
Also Read: Types of Operators in C: Roles, Usage & Best Practices 2025
Now that you understand how overflow and underflow impact the softmax function, let’s look into how integer overflows happen in common operations and typecasting in C.
How Do Integer Overflows Happen?
Integer overflow can occur in various situations, such as arithmetic operations, typecasting, handling user input, and loops. In each of these cases, the result of an operation exceeds the maximum or minimum value that can be stored in a variable, causing unexpected behavior or errors.
Let's explore these situations with code examples, explanations, and their outputs:
1. Arithmetic Operations: Addition and Multiplication
Addition Overflow Example: In arithmetic operations like addition, if the result exceeds the maximum value the data type can hold, it causes an overflow.
#include <stdio.h>
int main() {
int a = 2147483647; // Maximum value for a signed int
int b = 1;
int result = a + b; // Overflow occurs here
printf("Result: %d\n", result); // This will cause an overflow
return 0;
}
Explanation: Here, a is assigned the maximum value a signed integer can hold (2147483647). Adding 1 to it results in 2147483648, which exceeds the maximum value and causes an overflow.
Output:
Result: -2147483648
Result: The result wraps around, and instead of a large positive number, the result is a negative value due to overflow.
Multiplication Overflow Example: Overflow can also occur in multiplication when the result exceeds the maximum value for the data type.
#include <stdio.h>
int main() {
int a = 32767; // Maximum value for a signed short
int b = 1000; // A large multiplier
int result = a * b; // Overflow occurs here
printf("Result: %d\n", result); // This will cause an overflow
return 0;
}
Explanation: Here, a is the maximum value for a signed 16-bit integer (32767), and multiplying it by 1000 results in a value too large to fit into the int data type, causing an overflow.
Output:
Result: -7273792
Result: The multiplication result exceeds the range of the int type and wraps around to an incorrect, negative value.
2. Typecasting Overflow
When casting a larger data type into a smaller one, the value can exceed the range of the smaller type, resulting in overflow.
#include <stdio.h>
int main() {
long a = 2147483647; // Large value for a long integer
int b = (int)a; // Typecasting long to int, overflow occurs
printf("Result: %d\n", b); // This will cause an overflow
return 0;
}
Explanation: In this case, the long variable a holds a value larger than the maximum int can handle (2147483647). When we cast it to an int, it overflows because the int type cannot store values larger than 2147483647.
Output:
Result: -2147483648
Result: The overflow causes the result to wrap around, resulting in an unexpected negative number due to the limits of the int data type.
3. Handling User Input
When handling user input, if the input exceeds the data type's maximum range, overflow can occur.
#include <stdio.h>
int main() {
int a;
printf("Enter a value: ");
scanf("%d", &a); // User input for an integer
int result = a * 10; // Multiplying the input by 10
printf("Result: %d\n", result);
return 0;
}
Explanation: If the user enters a value larger than the maximum allowed for an int, overflow can occur when performing operations on the input.
Output Example 1:
Enter a value: 2147483647
Result: 21474836470 // Overflow, incorrect result
Output Example 2:
Enter a value: 1000000000
Result: -2147483648 // Overflow occurs due to exceeding the max int range
Result: If the input exceeds the int range (e.g., over 2.1 billion), multiplying it by 10 will cause overflow, resulting in a wrong value, which might even wrap around into negative values.
4. Iterations and Loops
Overflow can happen in loops if a counter variable exceeds the maximum value during iteration. For example, a counter variable in a loop can overflow if it keeps incrementing without proper bounds checking.
#include <stdio.h>
int main() {
int i;
for (i = 0; i >= 0; i++) { // Loop will eventually overflow
if (i == 5) {
break;
}
}
printf("Result: %d\n", i); // Overflow occurs when i exceeds int max
return 0;
}
Explanation: The loop continues incrementing i from 0 until it overflows, causing an unexpected result after the counter exceeds the maximum value.
Output:
Result: -2147483648 // Overflow happens and the loop breaks
Result: After a certain number of iterations, i exceeds the maximum value for an int, causing overflow and wrapping the value back to a negative number.
In all of these cases, the result can wrap around, leading to incorrect values. Preventing overflow requires careful bounds checking, using the correct data types, and validating user input.
Also Read: Data Types in C and C++ Explained for Beginners
Similarly, it’s important to understand how Integer Underflows occur, as this can lead to unexpected behavior and bugs in your C programs.
How Do Integer Underflows Happen?
Integer underflow occurs when a value becomes too small to be represented by a given data type, causing it to "wrap around" to the maximum value for that data type.
This can lead to unexpected behavior or errors, especially when working with arithmetic operations, typecasting, handling user input, and loops.
Let's explore these situations with examples and explanations:
1. Arithmetic Operations: Subtraction and Division
Subtraction Underflow Example: Underflow can occur when subtracting a number that is too large, resulting in a value smaller than the minimum value the data type can hold.
#include <stdio.h>
int main() {
int a = -2147483648; // Minimum value for a signed int
int b = 1;
int result = a - b; // Underflow occurs here
printf("Result: %d\n", result); // This will cause underflow
return 0;
}
Explanation: Here, a is assigned the minimum value a signed integer can hold (-2147483648). Subtracting 1 from it produces a value smaller than the minimum representable value, causing an underflow.
Output:
Result: 2147483647
Result: The result wraps around and becomes the maximum positive value for an int due to underflow.
Division Underflow Example: Underflow can also occur in division if the result becomes too small to be represented.
#include <stdio.h>
int main() {
int a = 1;
int b = -2147483648; // Minimum value for a signed int
int result = a / b; // Underflow occurs here
printf("Result: %d\n", result); // This will result in underflow
return 0;
}
Explanation: Here, the division of 1 by a very large negative number causes the result to be a very small value, which might be rounded to zero, causing underflow.
Output:
Result: 0
Result: In this case, the division results in a value too small to be represented, leading to underflow (effectively zero).
2. Typecasting Underflow
Underflow can also happen during typecasting when converting a large number from one type to another smaller type. If the number is too small for the target data type, underflow occurs.
#include <stdio.h>
int main() {
long a = -2147483649; // A value too small for an int
int b = (int)a; // Typecasting from long to int
printf("Result: %d\n", b); // This will cause underflow
return 0;
}
Explanation: Here, a is a long with a value smaller than what an int can represent. When casting to int, the value overflows and wraps around due to underflow.
Output:
Result: 2147483647
Result: The underflow occurs, causing the value to wrap around to the maximum positive value for an int.
3. Handling User Input
Underflow can occur if the user enters a value that is too small for the variable’s data type. This is particularly risky if the input is used in calculations.
#include <stdio.h>
int main() {
int a;
printf("Enter a value: ");
scanf("%d", &a); // User input
int result = a - 10; // Subtraction that could cause underflow
printf("Result: %d\n", result);
return 0;
}
Explanation: If the user enters a value smaller than the minimum range for an int, subtracting from it can result in underflow.
Output Example 1:
Enter a value: -2147483648
Result: 2147483647
Output Example 2:
Enter a value: -1000000000
Result: -1000000010
Result: For the first example, the subtraction leads to underflow, while in the second case, the subtraction operates normally within bounds.
4. Iterations and Loops
When a loop continually decrements a variable, it can eventually go below the minimum value and cause underflow.
#include <stdio.h>
int main() {
int i = -2147483648; // Start with the minimum value for signed int
while (i > -2147483648) { // Loop condition based on underflow
i--; // Decrement operation causing underflow
}
printf("Result: %d\n", i); // Underflow occurs and wraps around
return 0;
}
Explanation: In this example, the variable i is initialized to the minimum value for an int. When the value decreases further, it wraps around to the maximum positive value, causing underflow.
Output:
Result: 2147483647
Result: The value underflows and wraps around, producing the maximum value for an int.
Also Read: String Function in C with Examples
With both overflow and underflow explained, let's explore how integer overflows or underflows can be exploited, especially in scenarios where security can be compromised.
How Can Integer Overflows or Underflows Be Exploited?
Integer overflows and underflows, while technical errors, can be exploited by attackers to manipulate program behavior or gain unauthorized access. By exploiting these vulnerabilities, attackers can bypass security, alter control flow, or corrupt data.
A common exploit is buffer overflow, where overflows and underflows are used to manipulate memory allocation, leading to security risks in systems involving memory management and user input.
Buffer Overflow Vulnerability
A buffer overflow occurs when data exceeds its allocated memory, overwriting critical values like function return addresses, allowing attackers to execute arbitrary code. By exploiting integer overflows or underflows in buffer size calculations, attackers can manipulate memory and control program execution.
1. How Integer Overflow Can Be Used in Buffer Overflow Attacks:
When a program allows user input to define the size of a buffer (for example, in arrays or strings), an attacker can manipulate the size calculation by causing an overflow, potentially overwriting memory that holds sensitive data or control structures.
Example of an overflow being exploited:
#include <stdio.h>
#include <string.h>
void vulnerable_function(char* user_input) {
int buffer_size = 256; // Expected buffer size
char buffer[256];
// Potential overflow if user_input exceeds buffer_size
strcpy(buffer, user_input); // No bounds check, vulnerable to buffer overflow
}
int main() {
char malicious_input[300];
memset(malicious_input, 'A', sizeof(malicious_input) - 1); // Attacker-controlled input
vulnerable_function(malicious_input); // Pass attacker input
return 0;
}
Explanation: In this code, the strcpy() function copies the user input into the buffer without checking the size of the input.
An attacker can exploit this vulnerability by providing input that is larger than the allocated buffer size, causing an overflow that overwrites adjacent memory regions.
Output:
*** stack smashing detected ***: terminated
2. How Integer Underflow Can Be Used in Exploits:
Integer underflows occur when a program attempts to subtract a value from a variable, and the result goes beyond the minimum value allowed by the variable's data type.
In some cases, underflow can lead to a situation where an attacker manipulates the program's flow by causing the program to operate with values that should have been invalid.
For instance, if a program uses a calculation like unsigned int x = x - 1; and the value of x is already 0, underflow can result in x becoming the maximum possible value (e.g., UINT_MAX), which might enable an attacker to bypass range checks or loop conditions, potentially leading to unauthorized access or system compromise.
Example of Underflow Exploit in Loop or Range Checking:
#include <stdio.h>
void process_data(unsigned int value) {
if (value < 100) {
printf("Processing...\n");
} else {
printf("Value too large, skipping...\n");
}
}
int main() {
unsigned int attacker_value = 0;
// Attacker exploits underflow to pass the range check
process_data(attacker_value - 1); // Underflow occurs
return 0;
}
Explanation: Here, the attacker_value is 0, and by subtracting 1, an underflow occurs, and value becomes the maximum possible value for an unsigned int (UINT_MAX).
This causes the program to incorrectly pass the condition if (value < 100), allowing the attacker to bypass the range check and manipulate the program's behavior.
How Attackers Exploit Overflows and Underflows in Real-World Attacks?
Handling overflow and underflow in C requires careful consideration as it can be exploited by attackers to manipulate program behavior, corrupt data, or execute arbitrary code. Exploiting these vulnerabilities can lead to significant security risks, including buffer overflow attacks and denial of service.
1. Arbitrary Code Execution: Integer overflows can overwrite memory in such a way that an attacker can inject their own code into the program's execution path. This can allow them to execute arbitrary code, potentially compromising the system and gaining unauthorized access.
Example: If an attacker causes an integer overflow when calculating the buffer size for an array, they might overwrite critical control data, such as the return address of a function. This could lead to the attacker being able to execute their code when the function returns.
2. Denial of Service (DoS) Attacks: Both overflows and underflows can be exploited to cause a program to crash. For example, underflowing a variable and causing a division by zero could lead to undefined behavior and cause a program to abort or behave unpredictably.
Example: If a program doesn't check for underflows and proceeds with operations, an attacker might provide inputs that trigger underflows, causing the program to crash or enter an infinite loop, denying service to legitimate users.
3. Data Integrity Issues: Overflows and underflows can lead to data corruption. For example, if an attacker can influence the outcome of a calculation, they may be able to corrupt data by causing an overflow, leading to incorrect outputs.
Example: In a financial system, an overflow might cause a negative balance to be represented as a large positive value, potentially causing financial discrepancies.
Also Read: Top 25+ C Programming Projects for Beginners and Professionals
To finish, you’ll learn how to detect and prevent integer overflow and underflow in C, ensuring your code remains secure, stable, and free from these issues.
Detecting and Preventing Integer Overflow and Underflow in C
Integer overflow and underflow in C can cause unexpected behavior and security vulnerabilities. Since C lacks automatic detection, developers must implement methods to identify and prevent these issues.
You can follow these techniques for appropriately handling overflow and underflow in c:
1. Compiler Warnings for Overflow and Underflow
One of the simplest ways to detect potential overflow or underflow in C is by enabling appropriate compiler warnings. Modern C compilers like GCC provide flags to help catch these conditions early during the compilation process.
Compiler Flags:
- -Woverflow: In GCC, this flag helps detect overflow and underflow issues. It triggers a warning whenever an overflow or underflow is detected in arithmetic operations or assignments.
- -Wall: This general flag enables a wide range of warnings, including potential overflow and underflow.
Example:
gcc -Woverflow -Wall -o program program.c
Using these flags will warn the developer about operations that may lead to overflow or underflow, giving insights into potential issues.
2. Static Code Analysis Tools
Static analysis tools help by analyzing the source code without executing it, and they can detect potential issues like integer overflow or underflow.
These tools analyze the program flow and identify conditions where arithmetic operations may exceed the limits of the data types.
Common Static Analysis Tools:
- Clang Static Analyzer: Part of the Clang compiler, it helps detect overflow, underflow, and other critical issues by analyzing the C source code.
- Cppcheck: A static analysis tool for C/C++ code that can detect memory issues, arithmetic overflows, and other vulnerabilities.
- SonarQube: A popular tool that supports various languages, including C, to detect bugs, vulnerabilities, and code smells.
These tools analyze the code structure and logic to detect risks without executing the code.
3. Runtime Checks
Runtime checks are important to prevent integer overflow or underflow during program execution. These checks allow you to verify whether an operation will exceed the limits of the data type at runtime.
How to Implement Runtime Checks? Use Explicit Boundaries
Before performing arithmetic operations (like addition, multiplication), ensure that the operands are within safe limits for the data type.
Example of Addition Check:
#include <stdio.h>
#include <limits.h> // For INT_MAX and INT_MIN
int safe_add(int a, int b) {
if ((b > 0 && a > INT_MAX - b) || (b < 0 && a < INT_MIN - b)) {
printf("Overflow detected!\n");
return -1; // Handle overflow
}
return a + b;
}
int main() {
int result = safe_add(2147483647, 1); // Test overflow
if (result != -1) {
printf("Result: %d\n", result);
}
return 0;
}
Explanation: In this example, we check whether adding b to a would exceed the maximum or minimum limits of the int data type. If so, we avoid performing the addition and handle the overflow scenario.
Output:
Overflow detected!
Handling Underflow: Similarly, for underflow conditions, check whether a subtraction operation will produce a value smaller than the minimum possible value of the data type.
Example of Underflow Check:
#include <stdio.h>
#include <limits.h>
int safe_subtract(int a, int b) {
if (b > 0 && a < INT_MIN + b) {
printf("Underflow detected!\n");
return -1; // Handle underflow
}
return a - b;
}
int main() {
int result = safe_subtract(-2147483648, 1); // Test underflow
if (result != -1) {
printf("Result: %d\n", result);
}
return 0;
}
Output:
Underflow detected!
Runtime checks detect overflows and underflows during execution, catching errors that are not apparent during compile time.
By adding runtime checks, your program can handle potentially dangerous calculations safely, ensuring correctness even when unexpected input or edge cases occur.
Best Practices to Prevent Overflow and Underflow
When working with large numbers, always choose data types that can handle them without overflowing. For instance, use int64_t instead of int when dealing with numbers larger than the typical range of int.
- Bounds Checking Before Operations: Always perform bounds checks before performing arithmetic operations that can potentially cause overflow or underflow. This ensures that the result stays within the valid range.
- Avoid Dangerous Functions: Avoid using unsafe functions like strcpy() or gets(), which do not check for buffer overflows. Use safer alternatives like strncpy() or fgets() to prevent buffer overflow vulnerabilities.
- Use Compiler and Static Analysis Tools: Enable compiler warnings (-Wall, -Woverflow) to catch potential issues at compile time. Also, use static analysis tools like Clang or Cppcheck to detect overflow and underflow risks early in the development process.
- Sanitize User Input: Always validate and sanitize user inputs to ensure they don’t exceed the limits of the data types. This prevents overflow from happening due to improper or malicious inputs.
By incorporating these techniques into your development process, you can ensure your programs are more robust, secure, and free from integer overflow and underflow issues.
Also Read: Command Line Arguments in C Explained
You now have a solid understanding of overflow and underflow in C. Test your knowledge with this quiz to see how well you grasp the concepts and its applications.
Quiz to Test Your Knowledge on Overflow and Underflow in C
Assess your understanding of integer overflow and underflow in C, including their causes, effects, and methods for prevention. Answer the following multiple-choice questions:
1. What happens when an integer overflows in C?
a) It wraps around to the minimum value for that data type
b) It causes the program to crash immediately
c) It causes a compiler error
d) It results in an undefined value
2. Which of the following is a common situation where overflow can occur?
a) Adding two large integers
b) Dividing a number by zero
c) Assigning a value larger than the maximum value of the data type
d) Both a and c
3. How can underflow occur in C?
a) When a large number is subtracted from a smaller number
b) When subtracting 1 from the smallest value for a signed integer
c) When a variable is multiplied by zero
d) All of the above
4. What is the typical result when an integer underflows in C?
a) The value wraps around to the maximum possible value for the data type
b) The value becomes zero
c) The program crashes
d) The value becomes NaN (Not-a-Number)
5. Which of the following methods can prevent integer overflow or underflow?
a) Using larger data types
b) Performing bounds checking before operations
c) Using compiler warnings for overflow/underflow detection
d) All of the above
6. What does the following code output, considering the limits of the int data type?
int a = 2147483647;
int b = 1;
int result = a + b;
printf("%d\n", result);
a) 2147483648
b) -2147483648
c) 2147483647
d) Error
7. Which of the following can cause an integer underflow in C?
a) Subtracting a negative number from a positive number
b) Dividing an integer by zero
c) Subtracting 1 from the minimum value of a signed integer
d) Multiplying two large numbers
8. What will happen if the following code is executed?
int a = -2147483648;
int result = a - 1;
printf("%d\n", result);
a) The program will print -2147483649
b) The program will print 2147483647
c) The program will print 0
d) The program will cause an overflow error
9. Which of the following is the best way to detect overflow or underflow at runtime?
a) Use the sizeof() operator
b) Compare operands against the data type’s maximum and minimum values before performing the operation
c) Use printf() to print values before and after calculations
d) Use exit() to terminate the program
10. What will the following code output, considering the behavior of the unsigned int data type?
unsigned int x = 0;
x = x - 1;
printf("%u\n", x);
a) 0
b) -1
c) 4294967295
d) Undefined behavior
Also Read: 25 Most Common C Interview Questions & Answers [For Freshers]
Well done on completing the quiz! To continue expanding your skills in C programming and stay ahead of the curve, consider upskilling with upGrad’s expert-led courses to learn more about advanced programming concepts and real-world applications.
Keep Upskilling with upGrad to Keep Up With Industry Trends
upGrad’s courses provide expert training in C programming, focusing on key topics like integer overflow and underflow, data type limits, and effective error handling. You’ll gain hands-on experience by solving practical challenges, such as detecting overflow/underflow, implementing runtime checks, and applying safe coding practices in real-world scenarios.
Below are some relevant upGrad courses to elevate your programming skills and advance your career:
- Data Structures & Algorithms
- Core Java Basics
- Learn Basic Python Programming
- JavaScript Basics from Scratch
- AI-Powered Full Stack Development Course by IIITB
You can also get personalized career counseling with upGrad to guide your career path, or visit your nearest upGrad center and start hands-on training today!
Similar Reads:
Explore C Tutorials: From Beginner Concepts to Advanced Techniques
Addition of Two Numbers in C: A Comprehensive Guide to C Programming
C Program to check Armstrong Number
Array in C: Introduction, Declaration, Initialisation and More
Exploring Array of Pointers in C: A Beginner's Guide
What is C Function Call Stack: A Complete Tutorial
Discovering C Operators: An Overview with Types and Examples!
C Enum Type: Definition and Practical Implementation
Factorial Program of a Number in C
15 Most Important Features of C Language
Fibonacci Series Program in C Using Recursion
How to Use the For Loop in C Effectively?
Format Specifiers in C Programming
FAQs
1. What happens when integer overflow occurs in C?
Overflow wraps the value around, leading to unexpected and incorrect behavior in calculations and variable assignments.
2. How does integer underflow affect floating-point calculations?
Underflow causes inaccuracies in floating-point calculations when an integer is cast to a float, potentially losing precision.
3. How do overflow and underflow behave in unsigned integers?
Unsigned integers overflow by wrapping around to zero but do not underflow since they cannot represent negative values.
4. How do low-level libraries handle overflow and underflow in C?
These libraries use range checks and custom error-handling to ensure overflow/underflow doesn't affect program execution.
5. Can attackers exploit overflow or underflow vulnerabilities?
Yes, attackers can manipulate overflow and underflow to bypass security, corrupt memory, or execute arbitrary code.
6. Why does typecasting large integers to smaller types cause underflow?
Typecasting from a larger integer type to a smaller one can cause truncation, resulting in underflow if the value exceeds the smaller type's range.
7. What is the impact of overflow/underflow in loop-based calculations?
Overflow or underflow in loop variables can result in infinite loops or incorrect iterations, causing erratic program behavior.
8. How does integer overflow/underflow affect array indices?
Overflow or underflow in array indices can lead to invalid memory access, causing buffer overflows or potential security risks.
9. Can both signed and unsigned integers experience overflow/underflow?
Both can overflow, but unsigned integers wrap to zero, while signed integers overflow unpredictably, often causing negative values.
10. How do compiler optimizations affect overflow and underflow detection?
Aggressive optimizations may skip overflow checks, but flags like -ftrapv can force compilers to detect overflow during runtime.
11. Do different platforms handle overflow/underflow differently in C?
Yes, platforms and compilers may have different ways of handling overflows, from warnings to undefined behavior or runtime exceptions.
-9cd0a42cab014b9e8d6d4c4ba3f27ab1.webp&w=3840&q=75)
Take a Free C Programming Quiz
Answer quick questions and assess your C programming knowledge


Author|900 articles published


upGrad Learner Support
Talk to our experts. We are available 7 days a week, 9 AM to 12 AM (midnight)
Indian Nationals
1800 210 2020
Foreign Nationals
+918068792934
Disclaimer
1.The above statistics depend on various factors and individual results may vary. Past performance is no guarantee of future results.
2.The student assumes full responsibility for all expenses associated with visas, travel, & related costs. upGrad does not provide any a.



